
The Ultimate all in one Decoy Plattform.
Deploy honeypots in minutes. Detect threats before they reach your real assets. Enterprise-grade deception technology, simplified.
SUPPORTED BY

HOW IT WORKS
Deception in Four Steps
Set up your sensor network in minutes. No complex configurations, no code required.
Deploy Decoys
Spin up realistic honeypots that mimic your production systems. Databases, APIs, file servers—all convincing traps.
Attract Attackers
Sensors appear as vulnerable entry points. When attackers probe your network, they find our decoys first.
Get Alerted
Instant notifications with full attack details. Know exactly who’s targeting you and how they’re trying to get in.
Stay Protected
Use threat intelligence to harden your real systems. Block attackers before they ever reach your assets.
Features
Everything You Need to Trap Threats
Built for security teams who want to stay ahead of attackers, not chase them.
One-Click Deployment
Launch sensors instantly across cloud, on-premise, or hybrid environments.
Historical Analysis
Track attack patterns over time. Identify trends and emerging threats.
Minimize False Positives
Every alert is real. Legitimate users never interact with honeypots.
Real-Time Monitoring
Watch attacks unfold live. Full packet capture and session recording.
Attacker Profiling
Build detailed profiles of threat actors targeting your organization.
Executive Reports
Beautiful dashboards and PDF exports for your security leadership.
OVERVIEW
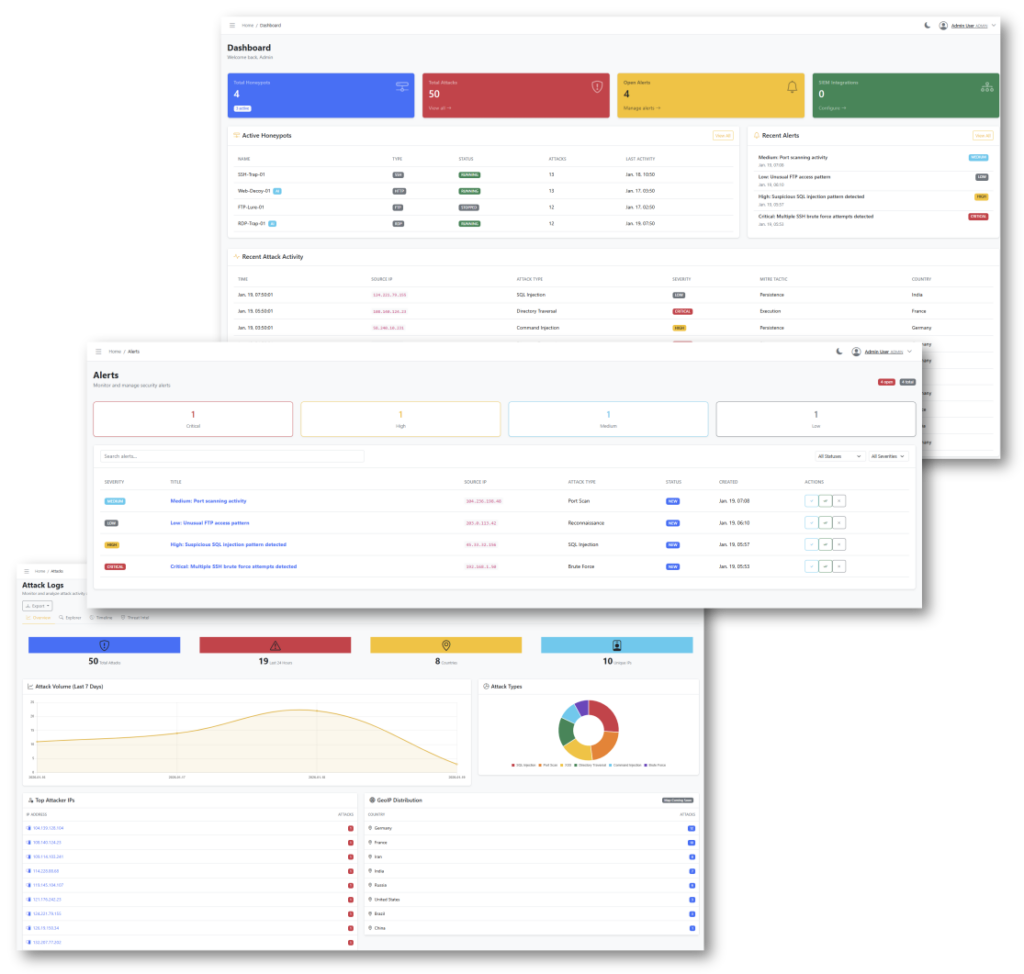
From intrusion to insight — in one platform.
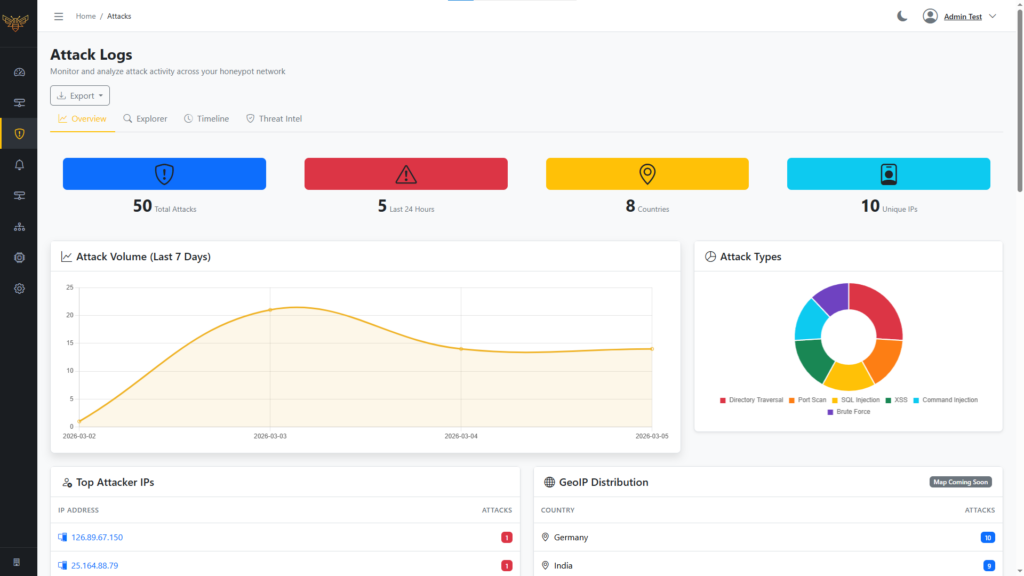
Hivesense captures real attacks and turns them into actionable intelligence.
Detect
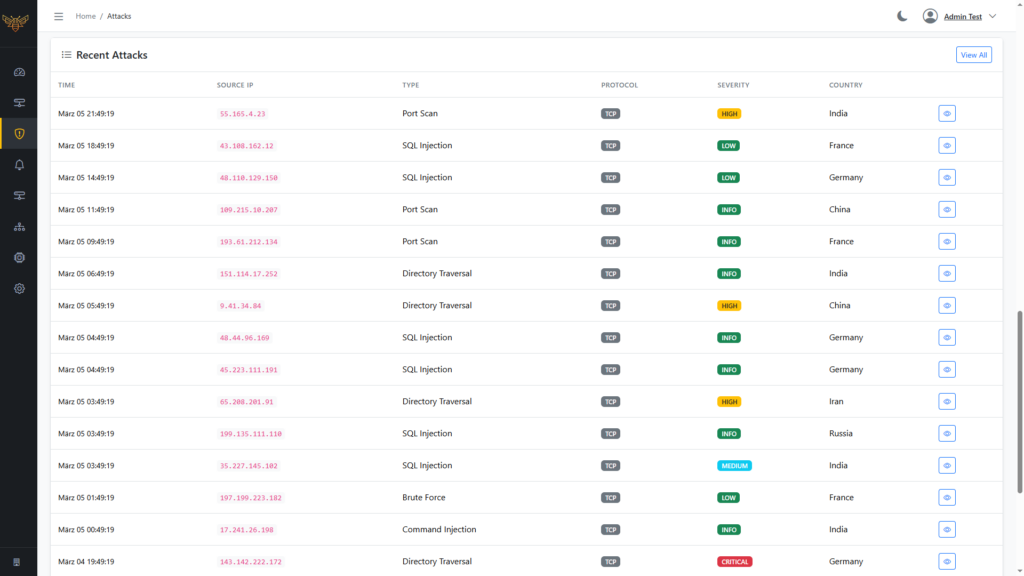
Live Attack Overview
Instantly see active intrusions, targeted decoys, and attacker activity across your environment — updated in real time.
Observe
Detailed Interaction Logs
Every connection, command, and movement is recorded with full context, enabling deep analysis without false positives.
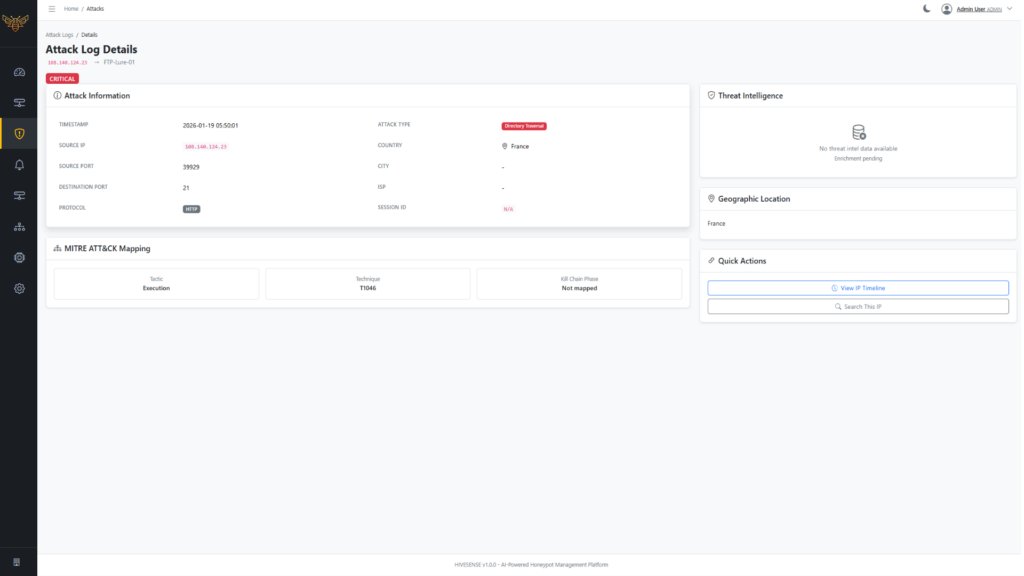
UNDERSTAND
Actionable Security Insights
Identify attack patterns, recurring tactics, and high-risk targets to strengthen defenses based on real attacker behavior.
